Hack the box OWASP Top 10: Baby todo or not todo
- carocsteads
- Feb 23, 2025
- 2 min read
Updated: Dec 9, 2025
Baby todo or not todo:
Synopsis: An application logic flaw results in compromised vertical privilege escalation, causing sensitive information to be exposed.
Skills Required:
Basic understanding of access control vulnerabilities.
Ability to analyze and understand source code.
Familiarity with the HTTP protocol.
Knowledge of basic scripting using a programming language such as Python.
Skills Learned:
Understanding the vertical access control vulnerability.
Familiarity with the process of exploiting access control vulnerability.
Experience in analyzing and understanding Burp messages to inject a payload.
The exercise: I'm so done with these bloody HR solutions coming from those bloody HR specialists. I don't need anyone monitoring my thoughts, or do I... ?

Analysis:
The application enables users to create a list of items and either mark them as completed or remove them.
Once the application submits a post to create a new item, it follows up with numerous get requests containing a secret.

A zip file can be downloaded. Upon opening, it displays a folder called Web Broken Authentication Control, which is then confirmed by the tab name.

We keep looking to identify if there is another clue. We see in index.html the following
index.html

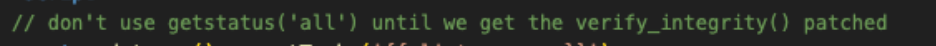

A comment indicates where to search for

Let's take a look at the util.py file where the verify_integrity() function is located.
Examine the @api.route('/list/all/') which does not include view arguments:
The first green arrow indicates the condition request.view.args ?
As api.route('/list/all/') lacks view arguments
The following green arrow points to whether request.isjson? it is not a JSON request,
Thus, api.route('/list/all/') proceeds directly to the red arrow check_secret(g.secret, g.user), skipping the verify_integrity() function.

Let's go to Burp and get the data-secret token with Get request /api/list/all to get the
flag.
From the original GET message

Let's try to add /all/ in the above GET message

The flag is presented.
How to prevent logic flow and privilege escalation:
Enforce server-side permission checks on all API endpoints
Verify access control on the server side instead of depending on client-side enforcement. Server-side validation guarantees that users cannot access unauthorized resources even if they alter their client. This approach centralizes security, making it more dependable and enforceable.
Deploy authorization middleware to verify user roles and permissions before executing sensitive operations.
Utilize JWTs (JSON Web Tokens) or session-based authentication to confirm user identities securely.
Implement Least Privilege Principles for user roles
Grant users only the essential permissions required for their role.
Clearly distinguish between admin and standard user functions.
Consistently evaluate user access rights and remove any unused privileges.
Regularly audit user access logs for anomalies
Record all events related to authentication and authorization.
Deploy automated monitoring to identify abnormal patterns (such as privilege escalations or unauthorized actions).
Establish alerts for unforeseen privilege modifications or an unusually high number of API requests from one user.
Comments